by ITLogixAdmin | Feb 6, 2019 | Breach, privacy, Security
Effectiveness of Phishing, Training & Understanding the Human Response Executive Summary Utilizing security awareness training and phishing security tests can be a useful and effective tool to reduce unintentional insider threats. However, if robust metrics are...
by ITLogixAdmin | Feb 6, 2019 | Ransomware, Security
A Short History of Ransomware The year 2014 may well go down in the history books as the year that extortion attacks went mainstream.” -Brian Krebs, security journalist “Fueled largely by the emergence of the anonymous online currency Bitcoin, these shakedowns are...

by ITLogixAdmin | Feb 6, 2019 | privacy, Security
Owning a small business means owning data. You’re constantly acquiring new information related to your customers, your financial details, and all the vendors and contractors with whom you work. One cyber criminal, though, one lucky hack, and you’ve just exposed your...
by ITLogixAdmin | Jan 16, 2019 | Ransomware, Uncategorized
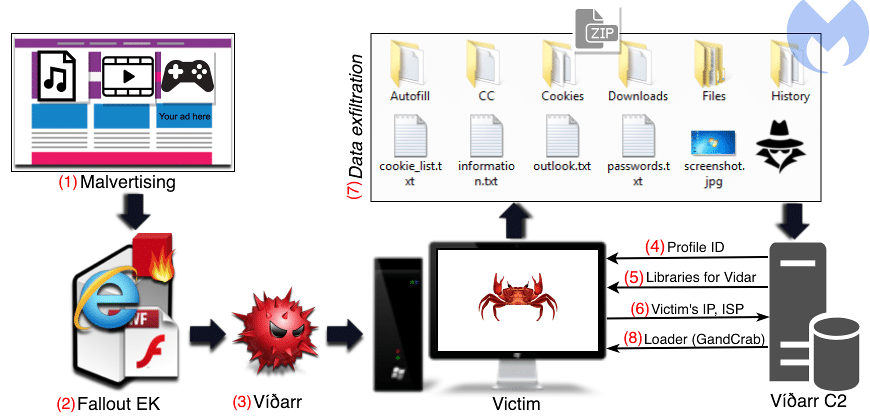
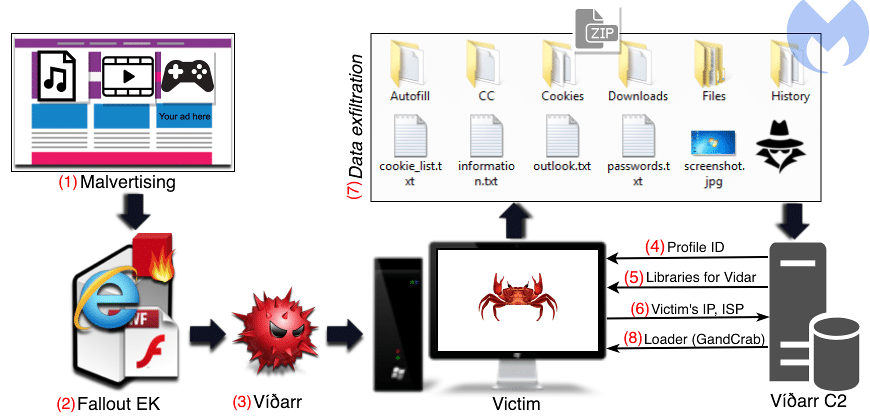
A new malware attack has been detected in the wild. This nasty combines two known pieces of malware: the Vidar data harvesting malware followed by GandCrab ransomware. Vidar exfiltrates a wide variety of data, including passwords, documents, screenshots, stored 2FA...

by ITLogixAdmin | Nov 15, 2018 | Backup, Office 365
In this article, we will be coveringMicrosoft Office 365 – the basicsHow secure your Office 365 data is against threatsWhy you should consider third-party backup Today’s Office 365 Landscape The suite of apps and services that comprise Office 365 today includes...


Recent Comments